Traditionally, a network firewall is a routed hop that acts as a default gateway for hosts that connect to one of its screened subnets. A transparent firewall (or Layer 2 firewall), on the other hand, acts like a “stealth firewall” and is not seen as a Layer 3 hop to connected devices.
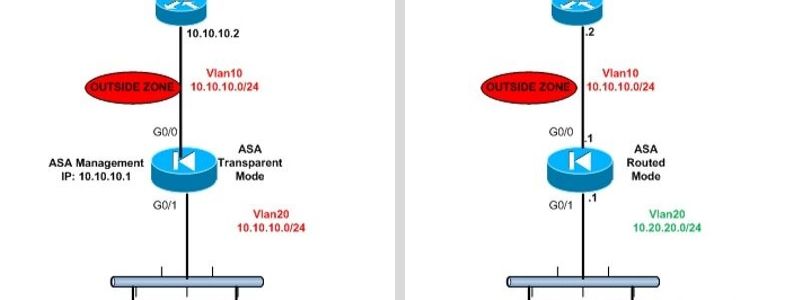
The appliance connects the same Layer 3 network subnet on its inside and outside ports, but each interface of the firewall resides in a different Layer 2 Vlan. The Cisco ASA firewall can operate both in Routed Firewall Mode (default mode) or in Transparent Firewall Mode.
Routed Firewall Mode:
See the diagram below for a common network topology of a Cisco ASA firewall working in Routed Mode.
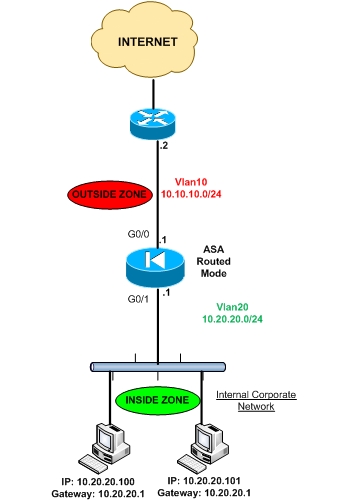
As you can see, there are two different network subnets. Inside network (10.20.20.0/24) and Outside Network (10.10.10.0/24).
There must be also two different layer2 vlans (Vlan20 for inside network and Vlan10 for outside network). All hosts residing in internal network must belong to subnet 10.20.20.0 and must have default gateway the internal IP of the ASA (10.20.20.1).
Transparent Firewall Mode:
The diagram below shows an example topology using a Cisco ASA in Layer 2 transparent mode.
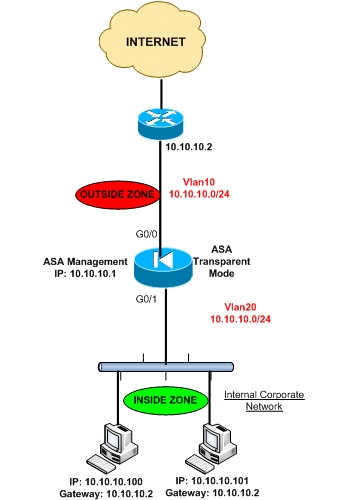
As you can see, there is only one Layer 3 network (10.10.10.0/24) BUT there MUST be two different Layer 2 Vlans (Vlan20 for inside zone and Vlan10 for outside zone).
All hosts must reside in network range 10.10.10.0 and the devices must have as default gateway the IP address of the outside router (10.10.10.2).
Also, a management IP address MUST be configured on the ASA firewall (again within the range of 10.10.10.0). DO NOT specify the management IP address of the ASA as the default gateway for connected devices.
Characteristics of Transparent Mode
• Transparent firewall mode supports only two interfaces (inside and outside)
• The firewall bridges packets from one VLAN to the other instead of routing them.
• MAC lookups are performed instead of routing table lookups.
• Can run in single firewall context or in multiple firewall contexts.
• A management IP address is required on the ASA.
• The management IP address must be in the same subnet as the connected network.
• Each interface of the ASA must be a different VLAN interface.
• Even though the appliance acts as a Layer 2 bridge, Layer 3 traffic cannot pass through the security appliance from a lower security level to a higher security level interface.
• The firewall can allow any traffic through by using normal extended Access Control Lists (ACL).
Initial Configuration
Asa(config)# firewall transparent
!Configure management IP below
Asa(config)# ip address 10.10.10.1 255.255.255.0
Asa(config)# interface Ethernet0/0
Asa(config-if)# nameif outside
Asa(config-if)# security-level 0
!
Asa(config)# interface Ethernet0/1
Asa(config-if)# nameif inside
Asa(config-if)# security-level 100
Related Posts
- Prevent Spoofing Attacks on Cisco ASA using RPF
- Configuring Connection Limits on Cisco ASA Firewalls – Protect from DoS
- Configuring AAA Authentication-Authorization-Accounting on Cisco ASA Firewall (TACACS+, RADIUS)
- Cisco ASA Firewall Management Interface Configuration (with Example)
- How to Configure Access Control Lists on a Cisco ASA 5500/5500-X Firewall (with Examples)