A very popular scenario for small networks is to have a Cisco ASA 5505 as border firewall connecting the LAN to the Internet.
Administrators in such networks are usually encountered with requests from their users that are not very security conscious.
Such a request could be to allow Remote Desktop (RDP) access from the Internet to an internal Windows server (Outside to Inside).
This might be very helpful for users who want to work from home but I would not recommend it. If you have to implement such a scenario, I suggest that you put the Remote Desktop server in a DMZ and not directly in the internal network.
However, companies with limited budget might have purchased a Cisco ASA 5505 with basic license which restricts the creation of a DMZ Vlan (although you can create 3 Vlans, the third Vlan can only communicate with one of the other two Vlans but not both).
Diagram
So, let’s see a typical network topology with ASA 5505 basic license and an internal Remote Desktop server.
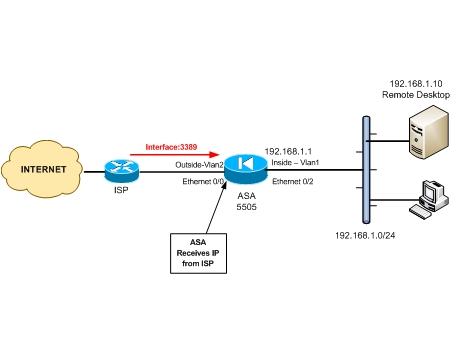
Again, I don’t recommend such a network topology as shown above. Remote Desktop machines are very prone to attacks, especially brute-force password attacks.
In windows, the administrator account does not get locked-out by default. So a brute force administrator password attack on the RDP server from remote attackers can be successful especially if the administrator password is weak.
In any case, if you are “forced” to implement such a scenario, here is the configuration:
Assume that the ASA receives IP address dynamically from the ISP (via DHCP protocol). So the outside IP of the ASA is not fixed.
Therefore, we will configure static NAT with port redirection using the outside interface. Since the outside address is dynamic, you can use a service such as DynDNS to get a fixed domain name irrespective of the IP mapped with it.
Configuration to Allow RDP from Outside on Cisco ASA
The following is a configuration snapshot for ASA versions prior to 8.3 and for ASA 8.3 as well.
ASA version prior to 8.3
ciscoasa(config)# static (inside , outside) tcp interface 3389 192.168.1.10 3389 netmask 255.255.255.255
ciscoasa(config)# access-list OUTSIDE-IN extended permit tcp any any eq 3389
ciscoasa(config)# access-group OUTSIDE-IN in interface outside
ASA version 8.3 and later
ciscoasa(config)# object network RDP_static
ciscoasa(config-network-object)# host 192.168.1.10
ciscoasa(config-network-object)# nat (inside , outside) static interface service tcp 3389 3389
ciscoasa(config)# access-list OUTSIDE-IN extended permit tcp any host 192.168.1.10 eq 3389
ciscoasa(config)# access-group OUTSIDE-IN in interface outside
NOTE: Notice that in version 8.3 we reference the Real IP address (192.168.1.10) in the access-list and not the mapped IP
Related Posts
- Prevent Spoofing Attacks on Cisco ASA using RPF
- Configuring Connection Limits on Cisco ASA Firewalls – Protect from DoS
- Configuring AAA Authentication-Authorization-Accounting on Cisco ASA Firewall (TACACS+, RADIUS)
- Cisco ASA Firewall Management Interface Configuration (with Example)
- How to Configure Access Control Lists on a Cisco ASA 5500/5500-X Firewall (with Examples)