We hear a lot about internet security and safety. But did you know that some security is built right into the protocol used to bring wireless service into your home or business?
The most prevalent wireless communication standard for home or business networks is of course the WiFi protocol (based on IEEE 802.11 framework).
Since WiFi involves data communication over the open air, the creators of this protocol embedded security and encryption in the standard from the very beginning.
However, not everything was roses in terms of WiFi security at the beginning of its era as we will discuss below.
In this article we will describe the different types of WiFi security and explain which one you should use in your own home or business WiFi network.
Why WiFi Security is Important
Along with all the websites, email platforms, and streaming services that are accessed from your devices are opportunities to invade your privacy or steal your data.
Internet security, as a whole, must be implemented end-to-end by adding layers of secure features that prevent data leaks and theft.
Starting from the user’s device (i.e smartphone, laptop computer, home smart device etc), the communication with the rest of the network must be encrypted and secured.
Especially if this first-line communication is over a wireless network (whereby everyone, even outside your home, can “sniff into”) then strong encryption and security are extremely important.
That’s why WiFi security must be taken into consideration when implementing or using a wireless home network.
Let’s now see what WiFi security options are out there.
Types of WiFi Security
Internet security has been around for almost as long as the internet itself. It has also been through a number of upgrades and changes since WiFi wireless became the main standard in the late 1990s.
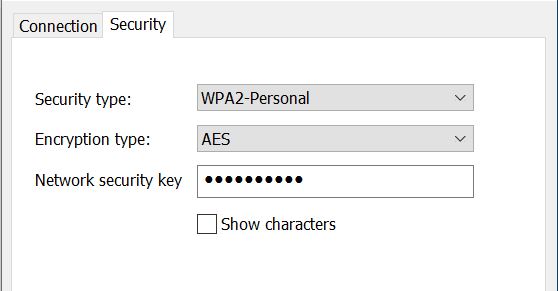
When you have a new router installed, you usually just follow the instructions for plugging it in and resetting your password.
But, how much attention is paid to the little acronyms that describe the type of security protocol used to protect your signal?
Those three little letters can make a huge amount of difference in the quality of your service and the limits of its protection. Read on to learn about the different types of wifi security protocols.
Wired Equivalent Privacy (WEP)
In the old days of WiFi, the Wired Equivalent Privacy protocol was normally the first option you saw when configuring your router and establishing a connection for the first time.
It was meant to mimic the standard used for wired services, and it’s one of the oldest and most widely used security protocols in existence.
However, the age of this standard and built-in restrictions made it vulnerable to hacking and data leaks.
There is a 256-bit version of this standard available, but most routers that use this standard remain at a 125-bit level. WEP relies on a fixed key system to protect data packets in transit.
Shortly after its introduction, a number of proof-of-concept exploits highlighted how easy WEP is to hack, and the Wi-Fi Alliance retired it and ended support in 2004. If you still have a router using WEP, upgrade or replace it.
Wi-Fi Protected Access (WPA)
Wi-Fi Protected Access was the first new security protocol released in response to the issues discovered with WEP.
It was formally adopted by the Wi-Fi Alliance in 2003, the year before support for WEP ended. The most common WPA configuration is WPA-PSK, which stands for Pre-shared key.
The keys used to encrypt data with this protocol set 256-bit encryption as their standard.
Other than that, the two major improvements over WEP are message integrity checks and the Temporal Key Integrity Protocol (TKIP).
However, because it’s based on the original WEP technology, it’s still subject to some of the same vulnerabilities,
TKIP was the original upgrade for this security protocol. It improved on WEP by using a per-packet encryption standard that’s more secure than a fixed key system. It has since been improved farther via the Advanced Encryption Standard (AES).
The integrity checks analyze data as it passes from the access point to the client in order to determine if any of the packets have been altered or captured in-transit.
WPA is still considered not secure in WiFi networks. If you have WPA configured we recommend to change it to WPA2 (see below).
Wi-Fi Protected Access II (WPA2)
In 2006, the next generation of WPA was introduced. WPA2 made the AES algorithm mandatory and introduced another security standard, Counter Cipher Mode with Block Chaining Message Authentication Code Protocol, or just CCMP for short.
The main and nearly lone vulnerability in this standard requires the attacker to have access to the network before the exploit can occur.
Once the network is accessed, the hacker can access the security keys and proceed with the attack. This means there really is only a concern among enterprise-level WI-Fi rather than home or smaller networks.
The best prevention for such attacks on you business network is to disable the Wi-Fi Protected Setup (WPS) and flash the access point to a distribution that doesn’t support WPS, if possible.
Wi-Fi Protected Access III (WPA3)
This is the newest generation of Wi-Fi security protocols, released in 2019. How does it improve upon Gen 2?
It makes wireless network harder to hack on public networks. This is an especially important point when you consider that more and more companies are using remote work forces and public Wi-Fi.
WPA3 offer higher encryption standards for more robust data harvesting protection.
Networks using this standard are also easier to log on to, and the connected devices are never displayed.
WPA3 also includes enhanced protection against common exploits like brute force attacks.
With the release of the newest WiFi6 generation (802.11ax), WPA3 will play a significant role in wireless security since the newest standard supports connections of many more devices in a single network (such as airports etc), therefore WPA3 will protect all these devices from a variety of attacks.
Additional Security Tips for Your WiFi Connection
Your wireless security begins with using the most current firmware and encryption standards available, but it shouldn’t end there.
You can improve your security and run everything from your home computer or your home IoT devices with peace of mind by incorporating these other security best practices.
- Create strong, unique passwords and change them regularly. WiFi passwords should be at least 20 characters long and preferably having numbers, letters and special characters in them.
- Change the default SSID name of your network. Hackers tack exploits that are particular to known networks, routers, and service providers. Removing the default SSID masks who’s providing your service.
- Unplug your router when you’re not at home or at work.
- Change your security protocol if it’s using an older standard. For example, upgrading from WPA to WPA 2 or better to WPA3. However, WPA2 will be sufficient if you use a really strong wifi key (password) as recommended in point 1 above.
- Change your default router IP address for the same reasons listed above.
- Install a VPN on your router to add encryption and other safety features. This will also mask your identity, activity, and location.
Final Thoughts
These days, WiFi is used for more than just surfing the internet. It connects your smartphone and many of the smart devices that make your home or office more comfortable and functional (such as smart locks, thermostats etc).
Our goal is to provide you with timely information about the technologies that power your world. The above information is intended to provide you with the facts you need to make educated decisions about privacy and security.
Leave a Reply