Even before 5G, meaning fifth-generation cellular data, has become a consumerist reality, there are already a host of concerns, mostly sprouting from pre-existing understandings of its predecessor 4G in light of recent exploitations of the particular network architecture that these connection modules use.
As opposed to traditional crime, where it constantly becomes exponentially harder to get away with it and much easier to combat it, cybercrime is one of the hardest criminal fields to counter.
It’s dominated by a combination of a progress-hungry tech field, releasing misunderstood or under-understood products to extremely knowledgeable cybercriminals and flailing cybersecurity regulations, privacy policy and a consumer base made up of people who are increasingly divorced from the realities of what it is that they are using.
This situation has led to a lot of issues and a lot of proposed solutions. So, let’s take a look at cellular data hacks and the role of multi-factor authentication.
Origins Of The Threat
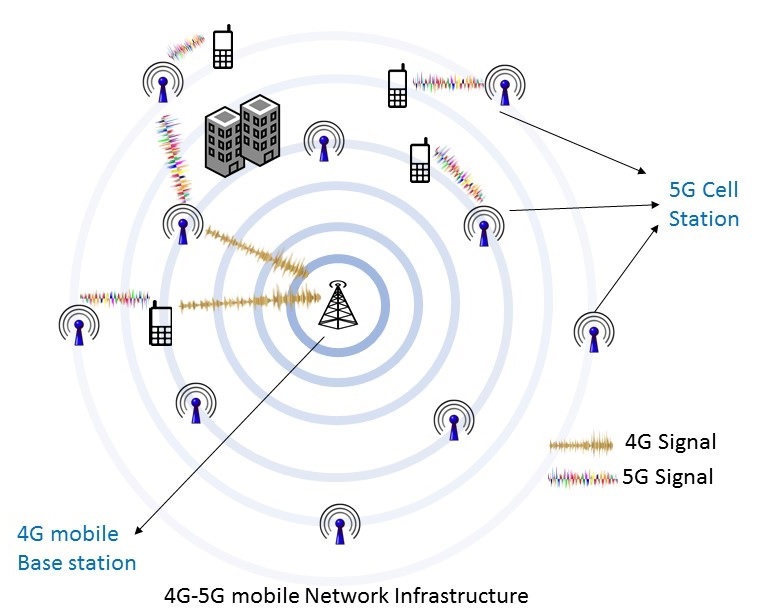
4G and 5G are both parts of a broader consumerist network technology, aimed, in almost every sense, to target laymen, with convenient, portable, high speed network access.
“It’s no secret that most people don’t understand technology”, writes James Harding, tech blogger at Australia2Write and NextCoursework.
“With technology which is so optimized and so packaged for consumption by everyday users, your chance of vulnerabilities being exploited is much higher from the get-go, since users won’t know what to look for or what to do to protect themselves. They hardly even know that the threat is out there to begin with.” So, as a technological field with a user knowledge-level far below average, you’ve already got an issue.
The other reason why this technology being a vital ingredient in a multi-trillion-dollar mobile industry is difficult related to progress.
Consumers, much to the chagrin of the smart-phone industry, don’t drop their old model the second the new one is available and instantly upgrade for great personal expense.
With the pace that the smartphone/smart-device industry develops, consumers would have to be upgrading constantly which, for devices now priced often around $1000 is impossible.
So, tech companies have to leave outdated tech models, network technology and a whole host of other outmoded pieces of software and hardware still out on the market.
This is a breeding place for cybercrime. Cybercriminals can use backdoors and antiquated vulnerabilities identified in weaker, older and more neglected software to access people’s private information at will, and it’s costly and difficult for the tech companies to put measures in place to stop this.
Convenience
Relating to the user-orientated realities of the tech industry, it’s also worth acknowledging that all technology which isn’t, in of itself, dedicated security software or being produced for tech companies to use themselves, is going to involve a trade-off between convenience/sleekness (sometimes incorrectly referred to as optimization) and security.
“When an industry is as user facing but complex as the technological field, it’s no wonder that problems are created. A product, in this day and age, which is a dream to use and has complete ease of access usually means there’s a lot of ease of access headed directly into the hands of criminals as well”, warns Louise Fox, website admin at BritStudent and WriteMyx.
Banks have the same issue, knowing that increasing the technological aspects to banking involves a much greater sense of risk. But whereas banks usually pay the rice of fraud committed against them, mobile companies tend to still be more interested in sales and appearance than truly rigorous security.
Two-Factor Authentication
The earliest indication that something can be done is through the somewhat clunky, very simple concept of two-factor authentication.
It’s a sort of step backwards in some ways, but it’s an excellent way of dealing with problems. It forces users to constantly have more proof than a singular access, by requiring them to back-up their login credentials with further information, which hackers won’t be as likely to have been able to get their hands on.
Conclusion
It will take time and a lot of work, but there is a definite sense in which there has been an improvement in the degree to which people take cybercrime seriously.
4G and 5G both present specifically tricky areas for security and may require imaginative solutions. In the meantime, there’s two-factor authentication to stem the tide.
Author

Working as a content marketer and editor at PhdKingdom and Academicbrits, Michael Dehoyos helps companies create effective marketing strategies. He is passionate about sharing his knowledge and expertise and does so through blogs like OriginWritings and other online publications.
Leave a Reply